In December, we introduced hosted PKI provider integration as a new way of authenticating devices with Golioth. Today, we’re happy to announce another step forward in device security with support for Identity Provider based authentication when connecting to your PKI provider.
The new authentication method takes advantage of OpenID Connect to allow you to grant Golioth access to your PKI provider without the need to create long term credentials. Although we’ll continue to support the existing access key based connection method, we recommend that all new designs utilize identity provider based authentication, as it allows Golioth to authenticate to AWS without storing any key material.
How does the identity provider work?
OpenID Connect is an open authentication standard built on top of OAuth 2.0, that allows web services to authenticate requests without any pre-shared key material. Golioth’s new ID Provider service allows your Golioth projects to authenticate themselves with JSON Web Tokens (JWTs) issued by Golioth’s internal ID Provider, allowing your project to make authenticated requests without storing an access key in Golioth’s backend.
JWTs are signed JSON objects that contain information about the holder of the token, as well as a URL external services can visit to verify the token’s authenticity. When a Golioth project wants to make an authenticated request to an external service, it can now make use of the new Golioth ID Provider service:
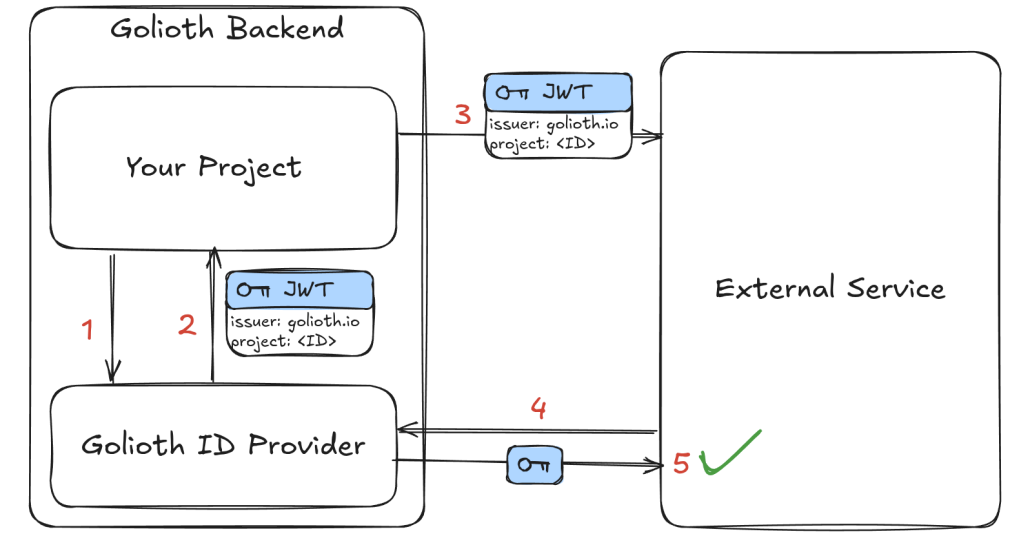
- Within Golioth’s backend, the project requests a JWT from Golioth’s ID Provider service.
- The ID Provider service issues a token containing the project’s ID, and signs the token with Golioth’s own signing key.
- The project attaches this token as a header when making a request to the external service it needs to talk to.
- The external service reads Golioth’s issuer URL from the token, and gets Golioth’s public key.
- The external service verifies the token signature with the public key, which proves that the request came from your project, and can proceed with the request.
For now, the ID Provider service is only enabled for PKI provider requests, but other services, such as pipelines will be able to authenticate with the ID provider service in the future.
No comments yet! Start the discussion at forum.golioth.io